Member-only story
Exploring a Lesser-Known Blockchain Vulnerability: Blockchain Forking Attacks | Karthikeyan Nagaraj
Understanding the Working Principle, Exploitation Methods, Prevention Strategies, and Impact of Blockchain Forking Attacks
Published in
4 min readMay 30, 2023
Introduction:
- Blockchain technology has gained significant attention for its potential to revolutionize various industries, providing transparency, security, and immutability.
- However, like any system, blockchains are not immune to vulnerabilities. While “51% attacks,” “double spend,” and other well-known vulnerabilities receive much attention, there exists a lesser-known yet significant threat called blockchain forking attacks.
- This article aims to delve into the intricacies of blockchain forking attacks, shedding light on their working principle, exploitation methods, prevention strategies, and the potential impact they can have on blockchain networks.
Working Principle of Blockchain Forking Attacks:
- Blockchain forking attacks exploit a fundamental characteristic of blockchain technology — its decentralized and distributed nature.
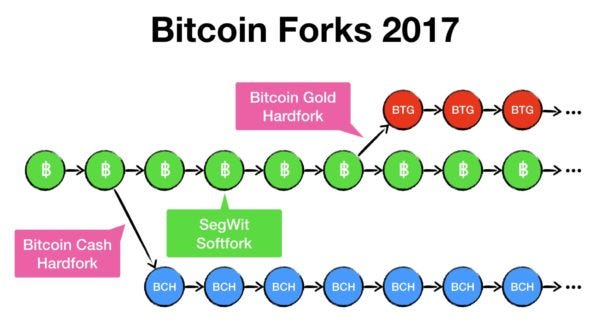
- A blockchain fork occurs when a group of participants diverges from the main blockchain, resulting in the creation of an alternative branch or version of the blockchain.
- Forking attacks involve intentionally causing a split in the blockchain network to gain control or manipulate the consensus mechanism.
How to Exploit Blockchain Forking Attacks:
1. Long-Range Attacks:
- An attacker secretly mines a parallel chain from an earlier block, attempting to surpass the main chain’s length.
- The attacker then releases their longer chain, causing the network to switch to this alternate version, nullifying previously confirmed transactions.
2. Time Warp Attacks:
- Similar to long-range attacks, time warp attacks exploit the blockchain’s consensus mechanism to manipulate block timestamps.

