Member-only story
Exploring the Porta Cipher: A Comprehensive Guide
Understanding the Features, Encryption Process, Decryption Process, and Use Cases of the Porta Cipher | Karthikeyan Nagaraj
3 min readApr 17, 2023
Introduction:
- The Porta Cipher, also known as the Porta Square or Porta Rectangle, is a polygraphic substitution cipher that was first introduced by Italian cryptographer Giovanni Porta in 1563.
- It is a simple yet effective cipher that is widely used in various applications, including military communications, banking, and personal messaging.
- This article aims to provide a comprehensive guide to the Porta Cipher, including its key features, encryption process, decryption process, and use cases.
Key Features of the Porta Cipher:
- The Porta Cipher is a polygraphic substitution cipher, meaning it replaces groups of letters rather than individual letters.
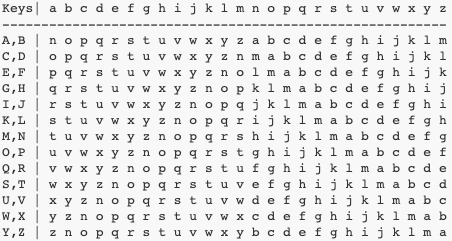
- It uses a tabula recta, also known as a Vigenère square or Vigenère table, to perform the substitution.
- The key to the Porta Cipher is a word or phrase that is repeated until it is the same length as the plaintext.
- The Porta Cipher is a symmetric key cipher, meaning the same key is used for both encryption and decryption.
Use Cases of the Porta Cipher:
- The Porta Cipher was widely used during the American Civil War by both the Union and Confederate armies to encode messages.
- It was also used by European banks to protect financial information.
- The Porta Cipher has been used by individuals for personal messaging and as a fun way to encrypt messages.
Encryption Process of the Porta Cipher:
- Choose a key word or phrase.
- Repeat the key word or phrase until it is the same length as the plaintext.
- Align the key word or phrase with the plaintext.
- Use the tabula recta to find the cipher text for each group of letters in the plaintext.
- Repeat step 4 for each group of letters…
