Member-only story
Understanding Hill Cipher: A Comprehensive Guide
Exploring the Key Features, Strengths, and Weaknesses of Hill Cipher | Karthikeyan Nagaraj
3 min readApr 4, 2023
Introduction:
- Hill Cipher is a popular symmetric key encryption algorithm that was developed by Lester S.
- Hill in 1929. It is a polygraphic substitution cipher that encrypts plaintext by dividing it into blocks of n letters and transforming those blocks using a matrix-based algorithm.
- Hill Cipher is widely used in various applications, including military communications, banking, and computer security.
- This article aims to provide a comprehensive guide to Hill Cipher, including its key features, strengths, and weaknesses.
Use Cases of Hill Cipher:
- Military communications: Hill Cipher has been used by the military to encrypt sensitive communications and protect them from interception.
- Banking: Hill Cipher has been used by banks to protect financial transactions and customer data from unauthorized access.
- Computer security: Hill Cipher has been used in various computer security applications, including encryption of passwords and other sensitive data.
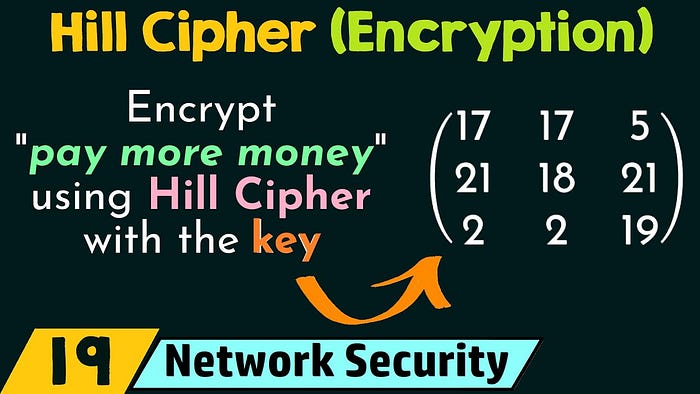
Encryption Process of Hill Cipher:
- Hill Cipher encrypts plaintext by dividing it into blocks of n letters and transforming those blocks using a matrix-based algorithm.
- The encryption algorithm involves multiplying the block of plaintext by a key matrix to produce a block of ciphertext.
- The key matrix used for encryption must be invertible, meaning that it has an inverse matrix that can be used for decryption.
Decryption Process of Hill Cipher:
- Hill Cipher decrypts ciphertext by multiplying the block of ciphertext by the inverse of the key matrix to produce a block of plaintext.
- The inverse matrix is calculated using matrix algebra and must exist for decryption to be possible.
- The decrypted plaintext is then reassembled from the blocks of n letters.
